How to Design Multi-Tenant Telecom Software for Hosting Providers and MVNOs
A Technical Guide to Designing Telecom Platforms for Hosting Providers and MVNOs
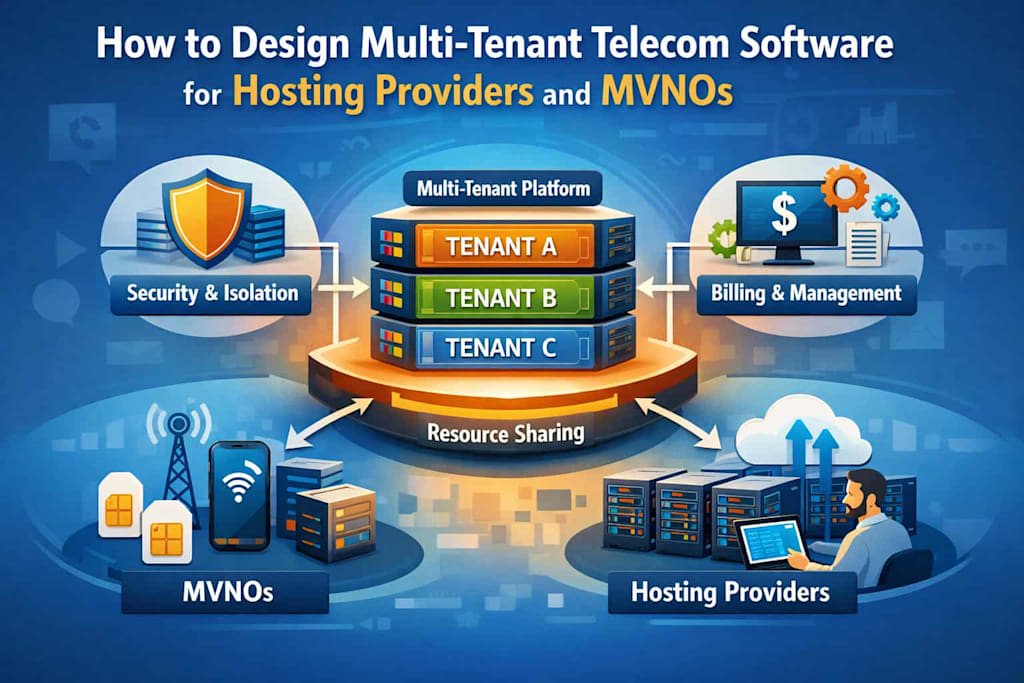
Designing multi-tenant telecom software is fundamentally different from building conventional SaaS platforms. It is not just about sharing infrastructure across customers—it is about enabling multiple independent telecom businesses to operate on top of a shared, highly constrained, and latency-sensitive system. When hosting providers enter the picture, the challenge becomes even more nuanced: the platform must satisfy both commercial flexibility for MVNOs and operational efficiency for infrastructure operators.
This duality shapes every architectural decision. What follows is a detailed, system-level exploration of how to design such a platform without collapsing under its own complexity.
Understanding the System You Are Actually Building
At first glance, the goal seems straightforward: build software that allows multiple telecom operators to coexist on a shared platform. In reality, you are designing a system with three distinct layers:
- A telecom execution layer that handles real-time operations such as calls, messages, and data sessions
- A business logic layer that manages billing, plans, and subscribers
- An infrastructure orchestration layer controlled by hosting providers
Each of these layers has different performance characteristics, ownership boundaries, and failure modes. The mistake many teams make is treating them as a single system. In practice, they must be decoupled but coordinated, which is far more difficult.
The hosting control panel naturally emerges at this boundary as a critical part of the control plane. It is the primary interface through which hosting providers interact with the system—managing tenants, allocating resources, configuring services, and observing system behavior. In a multi-tenant telecom environment, this UI is not merely a presentation layer; it acts as the operational gateway into the platform, translating infrastructure capabilities into actionable controls. Designing the system without explicitly accounting for this layer often leads to a disconnect between what the platform can do and what operators can realistically manage.
Multi-Tenancy Is a Spectrum, Not a Binary Choice
In most SaaS discussions, multi-tenancy is framed as a binary: either shared or isolated. Telecom breaks this simplification. Different tenants—especially MVNOs—have radically different requirements.
A small regional MVNO may prioritize cost efficiency and accept shared infrastructure. A large enterprise MVNO, on the other hand, may require strict data isolation, guaranteed performance, and even regulatory separation. This leads to an important realization: multi-tenancy must be configurable, not fixed.
The most effective architectures treat isolation as a policy layer, not a structural constraint. Instead of choosing one model, they allow tenants to exist along a continuum:
- At one end, tenants share compute resources and infrastructure, differentiated only by logical boundaries
- In the middle, tenants share compute but have isolated data stores and stricter quotas
- At the other end, tenants operate on effectively dedicated infrastructure while still benefiting from shared platform services
This flexibility is not just technically elegant—it is commercially essential. Hosting providers can align pricing tiers with isolation levels, turning architecture into a revenue lever.
Isolation: The Non-Negotiable Foundation
If there is one principle that cannot be compromised, it is isolation. In telecom systems, isolation failures are not minor bugs—they can result in data leaks, billing corruption, or regulatory violations.
What makes this particularly challenging is that isolation must exist simultaneously across multiple dimensions.
At the data level, tenant information such as subscriber records and call detail records must never leak across boundaries. At the compute level, one tenant’s workload must not starve another’s resources. At the network level, signaling traffic must be segmented to prevent interference or interception risks. Even configuration must be isolated—misconfiguring one tenant should never affect another.
The subtlety here is that isolation is not achieved by a single mechanism. It emerges from consistent enforcement across all layers. A perfectly isolated database is meaningless if application logic accidentally mixes tenant contexts. Likewise, compute isolation is insufficient if logging and observability pipelines aggregate data incorrectly.
The most robust systems treat tenant identity as a first-class concept, propagated through every request, every event, and every processing pipeline.
Separating Control Plane and Data Plane
One of the most critical architectural decisions in telecom systems is the separation between the control plane and the data plane.
The control plane is where business logic lives. It handles tenant onboarding, pricing configuration, subscriber management, and administrative operations. In practical terms, this layer is exposed to operators through the hosting control panel, which serves as the primary interface to the control plane. All provisioning workflows, tenant configurations, and service-level adjustments are executed through this UI, making it a critical translation layer between system capabilities and human actions. A well-designed control panel does not simply mirror backend APIs—it structures them into coherent operational flows, ensuring that complex telecom logic remains manageable for hosting providers and MVNO operators.
The data plane, in contrast, is where telecom operations actually occur. It processes calls, routes messages, and handles real-time data flows. It must be extremely fast, stable, and predictable.
Combining these two layers leads to inevitable problems. Business logic changes introduce instability into latency-sensitive operations, while performance optimizations in the data plane constrain flexibility in the control plane.
Separating them allows each to evolve independently. The control plane can adopt modern, flexible paradigms such as microservices and APIs, while the data plane can be optimized for throughput and low latency, often using specialized protocols and infrastructure.
For hosting providers, this separation is particularly valuable. It enables them to scale data plane components aggressively to handle traffic spikes, while keeping control plane resources stable and cost-efficient.
Designing for Event-Driven Reality
Telecom systems are inherently event-driven. Every call, message, or data session generates a stream of events that must be processed, stored, and often monetized.
Unlike traditional systems, where transactions are discrete and synchronous, telecom workloads are continuous and high-volume. Attempting to process everything synchronously leads to bottlenecks and system fragility.
Instead, modern architectures rely on event streaming and asynchronous processing. Usage events are ingested into a streaming platform, processed in pipelines, and consumed by downstream systems such as billing engines and analytics platforms.
This introduces a shift in thinking. Rather than asking, “Has this action completed?”, you ask, “Has this event been processed?”
This model also aligns well with hosting provider needs. Event-driven systems scale horizontally, distribute load naturally, and allow for failure isolation. If one component fails, events can be replayed without losing data integrity.
Billing: Where Architecture Meets Reality
Billing is often treated as a feature. In telecom, it is the system’s ultimate test.
The complexity arises from the need to translate raw usage into financial outcomes under highly variable conditions. Pricing models can include per-second billing, tiered data usage, bundles, promotions, and contractual agreements—all of which must be applied accurately and often in near real time.
A robust billing system separates rating (calculating the cost of usage) from invoicing (presenting charges to customers). This separation allows for reprocessing of historical data when pricing rules change, which is not uncommon in telecom.
For hosting providers, billing introduces an additional layer: infrastructure metering. CPU usage, storage consumption, and network bandwidth must be tracked and attributed to tenants. This effectively creates a dual billing system—one for telecom services and one for platform usage.
Designing these systems independently but allowing them to converge at the reporting layer is a practical approach that avoids unnecessary coupling.
Customization Without Fragmentation
MVNOs compete on differentiation. They want unique pricing models, branded experiences, and tailored service offerings. However, allowing unrestricted customization leads to fragmentation and operational chaos.
The solution lies in configuration-driven architecture. Instead of modifying code for each tenant, the system exposes flexible configuration layers that define behavior.
This approach requires discipline. It is tempting to introduce shortcuts—special cases for high-value tenants, custom logic embedded in services—but these quickly accumulate into technical debt.
A well-designed system treats customization as data, not code. Pricing rules, feature availability, and service behavior are all defined through configuration that can be versioned, validated, and deployed independently.
Observability in a Multi-Tenant World
Observability becomes significantly more complex in multi-tenant systems. It is no longer sufficient to know that the system is functioning—you must know for whom it is functioning, and at what level of quality.
This requires all telemetry—logs, metrics, traces—to be tagged with tenant context. Without this, diagnosing issues becomes guesswork.
For hosting providers, observability is directly tied to service level agreements. They must be able to answer questions such as:
- Which tenant is experiencing latency spikes?
- Which tenant is consuming disproportionate resources?
- Where are failures occurring within a specific tenant’s workflows?
Achieving this requires not just tooling, but architectural discipline. Every service must propagate tenant identity consistently, and every monitoring system must respect it.
Designing for Hosting Infrastructure Constraints
No matter how elegant your architecture is, it ultimately runs within the constraints of hosting infrastructure. These constraints—compute limits, network costs, storage performance—shape system behavior in ways that are often underestimated.
Stateless services become essential because they can scale horizontally and recover quickly from failures. Workloads must be carefully segmented to prevent high-demand tenants from overwhelming shared resources. In some cases, edge deployments are necessary to reduce latency for geographically distributed users.
Perhaps the most important consideration is predictability. Hosting providers need to understand how the system behaves under load. Unpredictable resource consumption is often more problematic than high consumption, because it makes capacity planning impossible.
Compliance as an Architectural Constraint
Telecom systems operate under strict regulatory environments. Requirements such as data retention, lawful interception, and regional data storage are not optional—they are mandatory.
In a multi-tenant system, these requirements vary by tenant. One MVNO may operate in a jurisdiction with strict data localization laws, while another may not.
This necessitates a flexible compliance architecture. Data storage must be region-aware, retention policies must be configurable, and audit trails must be comprehensive. These features cannot be bolted on later—they must be designed into the system from the beginning.
Front-End Architecture: The Overlooked Complexity
The frontend of a multi-tenant telecom platform is often underestimated. It is treated as a simple interface layer, when in reality it is a dynamic, tenant-aware control surface.
Unlike traditional applications, where the UI is relatively static, a telecom platform must adapt to:
- Different tenants with different branding
- Different roles with different permissions
- Different feature sets depending on configuration
This makes the frontend inherently complex.
A monolithic frontend quickly becomes unmanageable in this context. Changes for one tenant risk affecting others, and the codebase becomes tightly coupled to backend assumptions.
This is where microfrontend architecture becomes not just useful, but often necessary.
Microfrontends as a Structural Solution
Microfrontends allow the UI to be decomposed into independently deployable modules, each responsible for a specific domain such as billing, subscriber management, or analytics.
This mirrors the backend’s modular structure and allows teams to work independently. More importantly, it enables selective composition of the UI.
Different tenants can be presented with different combinations of modules. A small MVNO might only see basic subscriber management and billing, while a larger tenant might have access to advanced analytics and network controls.
This composability aligns perfectly with the configuration-driven philosophy discussed earlier.
Tenant-Aware UI Composition
To fully realize the benefits of microfrontends, the UI must be assembled dynamically based on tenant configuration.
This includes:
- Loading only the modules relevant to a tenant
- Applying tenant-specific branding (colors, logos, themes)
- Enforcing role-based access control at the UI level
The frontend effectively becomes a runtime composition engine, rather than a static application.
This approach also reduces deployment risk. Changes to one module do not require redeploying the entire application, and issues can be isolated more easily.
Backend-for-Frontend: Managing Complexity
As frontend complexity grows, direct interaction with backend services becomes inefficient. Different UI modules require different data shapes, and aggregating this data on the client side leads to excessive network calls and complexity.
The Backend-for-Frontend (BFF) pattern addresses this by introducing an intermediate layer that aggregates and tailors data specifically for frontend needs.
In a multi-tenant system, the BFF also plays a crucial role in injecting tenant context, enforcing access control, and optimizing performance.
Real-Time UX in Telecom Systems
Telecom platforms often require real-time or near-real-time interfaces. Operators need to see live call data, usage metrics, and system status.
This introduces additional challenges for frontend architecture:
- Efficient state management to handle streaming data
- Use of WebSockets or similar technologies for real-time updates
- Progressive loading strategies to avoid overwhelming the UI
The key is to balance responsiveness with performance. Not all data needs to be real-time, and overloading the UI with live updates can degrade usability.
Closing Perspective
Designing multi-tenant telecom software for hosting providers and MVNOs is less about choosing the “right” architecture and more about managing trade-offs deliberately.
You are constantly balancing:
- Isolation vs efficiency
- Flexibility vs maintainability
- Real-time performance vs system complexity
The systems that succeed are not those that optimize for one dimension, but those that remain adaptable as requirements evolve.
In the end, the true challenge is not technical—it is structural. You are building a platform where multiple independent businesses coexist, compete, and scale. The architecture must not only support this reality, but enable it.
About the Creator
Markus Koch
I am a professional IT consultant with 5+ years of experience.





Comments
There are no comments for this story
Be the first to respond and start the conversation.